Kód: 05088302
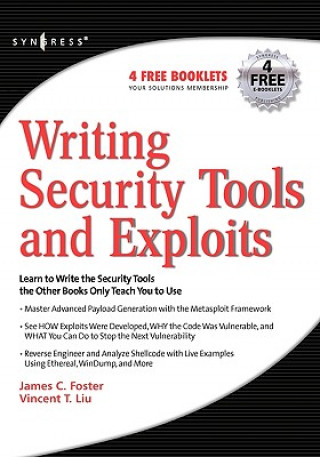
Writing Security Tools and Exploits
Autor James Foster
"Writing Security Tools and Exploits" will be the foremost authority on vulnerability and security code and will serve as the premier educational reference for security professionals and software developers. The book will have ove ... celý popis
- Jazyk:
 Angličtina
Angličtina - Väzba: Brožovaná
- Počet strán: 664
Nakladateľ: Syngress Media,U.S., 2006
- Viac informácií o knihe

Mohlo by sa vám tiež páčiť
-
The Graham Effect
10.52 € -27 % -
Akira 35th Anniversary Box Set
147.15 € -28 % -
The Millionaire Fastlane
33.92 € -
Turkish Short Stories for Beginners
11.23 € -25 % -
Mythographic Color and Discover: Magical Earth
14.07 € -25 % -
Kaiju No. 8, Vol. 6
7.89 € -25 % -
Children Of Dune
9.71 € -34 % -
Secrets of the Millionaire Mind
21.06 € -24 % -
Clash of Kings: The Illustrated Edition
27.74 € -28 % -
Hacking: The Art Of Exploitation
40.60 € -17 % -
Institute
10.93 € -26 % -
Good Night, Little Blue Truck
14.57 € -26 % -
New York School of Interior Design: Home
44.55 € -28 % -
Luna Coloring Book
13.46 € -24 % -
Into Thin Air
15.49 € -25 % -
Regenerative Leadership
35.54 € -2 % -
7000 Years of Jewellery
31.29 € -11 % -
Financial Planning & Analysis and Performance Management
50.73 € -24 % -
How to Be a Children's Book Illustrator
43.34 € -14 % -
Pomoc domowa
10.62 € -14 % -
Anya's Ghost
13.76 € -14 % -
US Army Small Unit Tactics Handbook
30.48 € -
English for Everyone: Phrasal Verbs: An ESL Book of Over 1,000 English Phrasal Verbs in Use
16.09 € -28 % -

Brock Biology of Microorganisms, Global Edition
85.37 € -9 % -
Anita Catita's Sewn Toy Treasures
12.75 € -25 % -
Look Alive Twenty-Five
8.40 € -26 % -
Podrecznik kart Lenormand
8.70 € -29 % -
Eylau-Friedland - la campagne de 1807
48.40 € -
MiG Aces of the Vietnam War
32.20 € -26 % -

University Physics with Modern Physics, Global Edition
90.84 € -10 % -
Oil Painting Techniques and Materials
16.20 € -24 % -
Complete Pottery Techniques
22.78 € -27 % -
Konosuba: God's Blessing on This Wonderful World!, Vol. 16
13.16 € -22 % -
Signature of All Things
9.71 € -4 % -
Tilda's Studio
12.95 € -46 % -
Audrey and Givenchy
17.41 € -19 % -
NOPI: The Cookbook
41.62 € -9 % -

Night Is Short, Walk on Girl
14.88 € -24 % -

SQL for Data Analytics
76.97 € -2 % -
The Witch Doesn't Burn in This One
11.33 € -26 % -
Fourth World by Jack Kirby Omnibus (New Printing)
167.51 € -4 % -
Cómic Los Futbolísimos 1: El misterio de los árbitros voladores
13.06 € -9 % -
Collected Stories
16.09 € -24 % -

Go Pro - German edition
12.75 € -16 % -
Last Hours: Chain of Iron
16.90 € -
Genesis
11.43 € -34 % -
Mit przedsiebiorczosci
16.09 € -
Polévky
4.24 € -31 % -
Friends: The One with the Surprises Advent Calendar
29.16 € -24 % -
Michael Schumacher
48.40 € -
England's Cathedrals
42.12 € -25 % -
Kate
16.09 € -24 % -
ITALIA
28.55 € -14 % -
Vignale
70.28 € -9 % -

Kredki Tropicolors Pudełko 12 sztuk
3.13 € -6 % -
Die Zwerge
12.65 € -10 % -
Our Beautiful World Color by Numbers
12.55 € -9 % -
ESG Matters
12.04 € -25 % -
Like Dreamers
16.90 € -24 % -
Upadek Númenoru
22.88 € -6 % -

Optimal Control Theory
31.19 € -25 % -
Dead Mother
59.04 € -
Mein erstes dickes Malbuch ab 2
4.55 € -
Devilman
12.95 € -9 % -
Scorcher: Hot Sexy Swimsuit Girls Models Pictures
14.88 € -7 % -

Field Guide to British Fish
26.93 € -4 % -
Easter Coloring Book for Kids Ages 4-8
9.41 € -2 % -
Mein Stickerbuch: Wie wachsen Obst und Gemüse?
7.79 € -

Out Of This World (Collector's Edition)
22.07 € -
Good House
13.46 € -24 % -

Commercium
185.84 € -
ATARI
44.66 € -

Geometrical Optics and Optical Design
319.54 € -
The Hand: The Demise of The Neanderthal
14.07 € -7 % -

Krisenmanagement
9.31 € -22 % -
Dublineses
20.04 € -
Two Hangmen, One Scaffold Book I. Baiting the Hangman
44.05 € -1 %
Darujte túto knihu ešte dnes
- Objednajte knihu a vyberte Zaslať ako darček.
- Obratom obdržíte darovací poukaz na knihu, ktorý môžete ihneď odovzdať obdarovanému.
- Knihu zašleme na adresu obdarovaného, o nič sa nestaráte.
Viac informácií o knihe Writing Security Tools and Exploits
Nákupom získate 137 bodov
 Anotácia knihy
Anotácia knihy
"Writing Security Tools and Exploits" will be the foremost authority on vulnerability and security code and will serve as the premier educational reference for security professionals and software developers. The book will have over 600 pages of dedicated exploit, vulnerability, and tool code with corresponding instruction. Unlike other security and programming books that dedicate hundreds of pages to architecture and theory based flaws and exploits, this book will dive right into deep code analysis. Previously undisclosed security research in combination with superior programming techniques will be included in both the Local and Remote Code sections of the book. The book will be accompanied with a companion Web site containing both commented and uncommented versions of the source code examples presented throughout the book. In addition to the book source code, the CD will also contain a copy of the author-developed "Hacker Code Library v1.0". "The Hacker Code Library" will include multiple attack classes and functions that can be utilized to quickly create security programs and scripts. These classes and functions will simplify exploit and vulnerability tool development to an extent never before possible with publicly available software. It provides readers with working code to develop and modify the most common security tools including Nmap and Nessus. You can learn to reverse engineer and write exploits for various operating systems, databases, and applications and, learn to automate reporting and analysis of security log files.
 Parametre knihy
Parametre knihy
Zaradenie knihy Knihy po anglicky Computing & information technology Computer networking & communications Network security
56.61 €
- Celý názov: Writing Security Tools and Exploits
- Autor: James Foster
- Jazyk:
 Angličtina
Angličtina - Väzba: Brožovaná
- Počet strán: 664
- EAN: 9781597499972
- ISBN: 1597499978
- ID: 05088302
- Nakladateľ: Syngress Media,U.S.
- Hmotnosť: 1216 g
- Rozmery: 227 × 180 × 46 mm
- Dátum vydania: 05. January 2006
Obľúbené z iného súdka
-
Web Application Hacker's Handbook: Finding and Exploiting Security Flaws 2e
36.86 € -25 % -
Nmap Network Scanning
43.85 € -7 % -

Practical Packet Analysis, 3e
51.95 € -
Hacker Playbook
31.59 € -
How to Speak Tech
23.79 € -24 % -
Tangled Web
42.43 € -26 % -

Stealing the Network: The Complete Series Collector's Edition, Final Chapter, and DVD
66.23 € -21 % -
Ghost in the Wires
17.01 € -24 % -
Practice Of Network Security Monitoring
52.96 € -9 % -

Wireshark 101
70.08 € -

UTM Security with Fortinet
59.44 € -

Foundations Of Information Security
35.64 € -25 % -
CISSP Practice Exams, Fifth Edition
32 € -18 % -

PowerShell and Python Together
32.10 € -24 % -

GSEC GIAC Security Essentials Certification All-in-One Exam Guide, Second Edition
59.14 € -18 % -

Wireshark Certified Network Analyst Exam Prep Guide (Second Edition)
42.22 € -

Wireshark Network Analysis (Second Edition)
98.13 € -
Python Ethical Hacking from Scratch
42.73 € -2 % -

Industrial Network Security
75.04 € -10 % -
Computer Forensics and Digital Investigation with EnCase Forensic v7
50.12 € -17 % -
Rootkit Arsenal: Escape and Evasion in the Dark Corners of the System
117.88 € -
Dawn of the Code War
19.13 € -19 % -
Cisco ISE for BYOD and Secure Unified Access
64.41 € -1 % -
Advanced Persistent Threat Hacking
50.12 € -17 % -

Network Security Through Data Analysis
42.43 € -24 % -
Cisco ASA for Accidental Administrators
32.10 € -24 % -
Mobile Application Hacker's Handbook
58.13 € -1 % -

Network Forensics
66.74 € -
IoT Hacker's Handbook
38.88 € -25 % -
Arista Warrior
56 € -25 % -
Google Cloud Certified Professional Cloud Network Engineer Guide
47.29 € -1 % -

Applied Network Security Monitoring
51.04 € -
We Are Anonymous
20.75 € -17 % -

Mastering Kali Linux for Advanced Penetration Testing
53.67 € -1 % -
VMware vSphere Essentials
47.29 € -1 % -

IPv6 Security
51.75 € -14 % -

Kali Linux Cookbook
81.52 € -1 % -
Configuring Juniper Networks NetScreen and SSG Firewalls
46.78 € -9 % -
Kali Linux - Assuring Security by Penetration Testing
47.29 € -1 % -
Wireshark for Security Professionals - Using Wireshark and the Metasploit Framework
38.88 € -25 % -

Security Power Tools
42.43 € -24 % -

Industrial Network Security
52.35 € -
Counterintelligence in a Cyber World
60.66 € -9 % -

Learning Network Forensics
53.67 € -1 % -
Quantum Key Distribution Networks
103.10 € -7 % -

Cisco ASA Configuration
65.93 € -18 % -

Information Assurance Handbook: Effective Computer Security and Risk Management Strategies
59.14 € -18 % -
Countering Cyberterrorism
175.11 € -7 % -

Guide to Enterprise Networking Technology
7.89 € -79 %
Osobný odber Bratislava a 12762 dalších
Copyright ©2008-26 najlacnejsie-knihy.sk Všetky práva vyhradenéSúkromieCookies



 24 miliónov titulov
24 miliónov titulov Vrátenie do mesiaca
Vrátenie do mesiaca 02/210 210 99 (8-15.30h)
02/210 210 99 (8-15.30h)